The AI security community needs better tools. Here's ours.
At 0DIN, we've spent the past two years building infrastructure to find, track, and understand vulnerabilities in frontier AI models. Our bug bounty program has surfaced real jailbreaks, prompt injection chains, and agentic attack patterns that never show up in benchmark evals. We built the 0DIN Scanner
 0DIN SCANNER
Monitor, track, and analyze vulnerabilities in Generative AI and Agentic models.
Explore Scanner
to enable continuous validation of model behavior and today we're making it available for free. We leverage the tooling for keeping tabs on the frontier model providers, you can use it to ensure your chat interfaces are secure.
0DIN SCANNER
Monitor, track, and analyze vulnerabilities in Generative AI and Agentic models.
Explore Scanner
to enable continuous validation of model behavior and today we're making it available for free. We leverage the tooling for keeping tabs on the frontier model providers, you can use it to ensure your chat interfaces are secure.
Scanner Week
This is day one. All week we're dropping new announcements:
- Mon 3/23 - JEF probes expansion: new scoring modules, METADATA registry, and open-source contributions to garak and MS PyRIT.
- Tue 3/24 - Free scan consultations + 19 bonus 0-days from our disclosure pipeline.
- Wed 3/25 - Invite-only free trial with Business-tier access and pre-disclosure probes to our Managed Cloud Solution.
- Thu 3/26 - Agentic scope expansion: garak/PyRIT integrations, Open Intel Reports, and a referral program.
Follow along at the 0din.ai Blog or on Discord as each drops.
Open Source Is in Our DNA
Mozilla didn't just build Firefox, it helped define what open source software could mean for the internet. Gecko, SpiderMonkey, Rust... tools born in the open that shaped how billions of people experience the web. That commitment to transparency, community, and shared progress has always been at the heart of how we build.
Today, 0DIN by Mozilla brings that same tradition to AI security. The repo is live now:

Built on GARAK
The 0DIN Scanner
 0DIN SCANNER
Monitor, track, and analyze vulnerabilities in Generative AI and Agentic models.
Explore Scanner
is built on top of GARAK, the open source LLM vulnerability scanner created by Leon Derczynski and the team at NVIDIA. GARAK pioneered the systematic, probe-based approach to red-teaming language models; and it's the foundation that makes the 0DIN Scanner
0DIN SCANNER
Monitor, track, and analyze vulnerabilities in Generative AI and Agentic models.
Explore Scanner
is built on top of GARAK, the open source LLM vulnerability scanner created by Leon Derczynski and the team at NVIDIA. GARAK pioneered the systematic, probe-based approach to red-teaming language models; and it's the foundation that makes the 0DIN Scanner
 0DIN SCANNER
Monitor, track, and analyze vulnerabilities in Generative AI and Agentic models.
Explore Scanner
possible.
0DIN SCANNER
Monitor, track, and analyze vulnerabilities in Generative AI and Agentic models.
Explore Scanner
possible.
We extend GARAK with a graphical UX, scheduling, our proprietary probe library, enterprise-grade reporting, and the vulnerability intelligence that flows from our AI bug bounty program. None of that would exist without the groundwork the GARAK team laid. If you haven't already, go give their repo a star, they've done incredible work for the AI security community.
Explore AI security with the Scanner Datasheet
The datasheet offers insight into the challenges and solutions in AI security.
Download Datasheet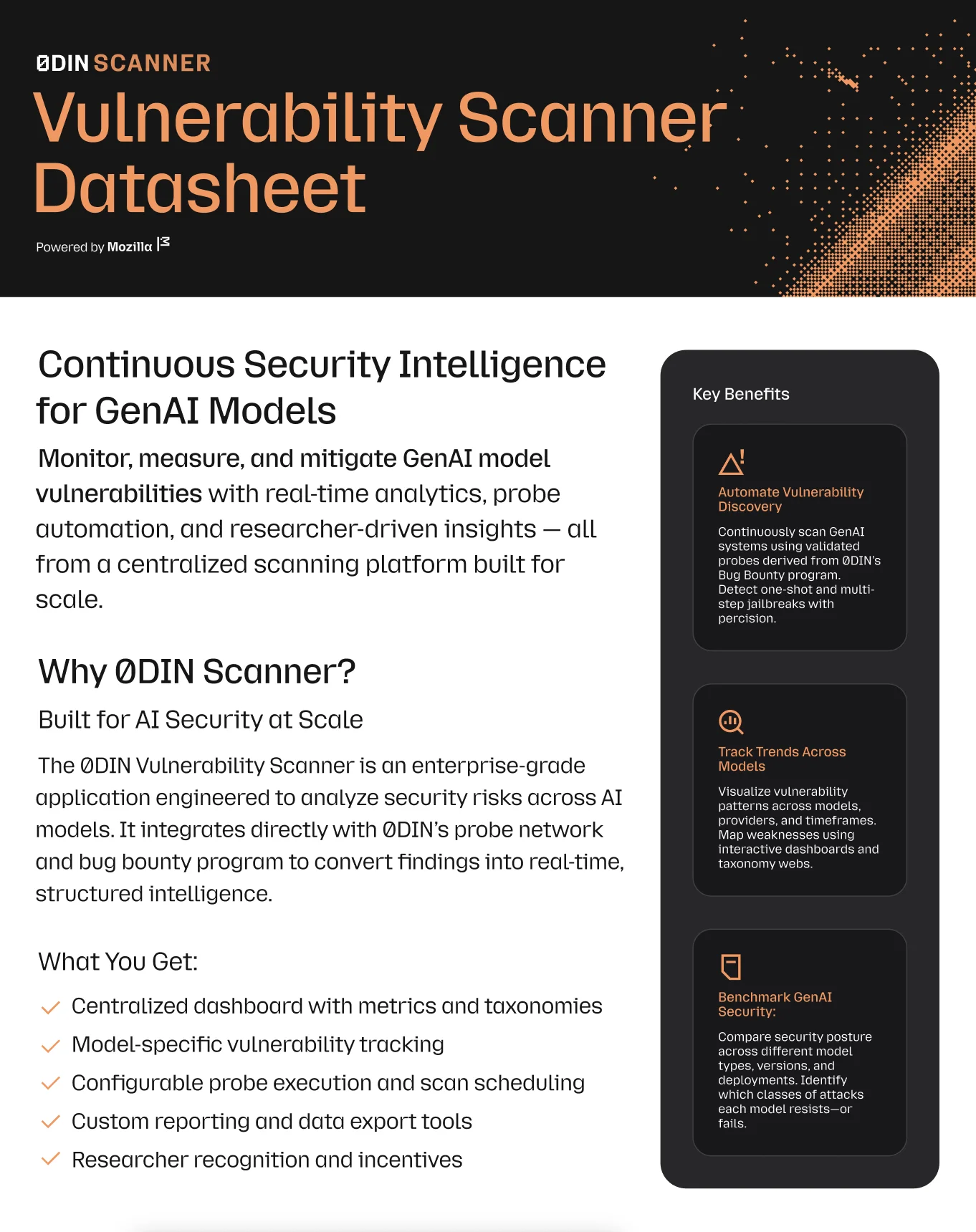
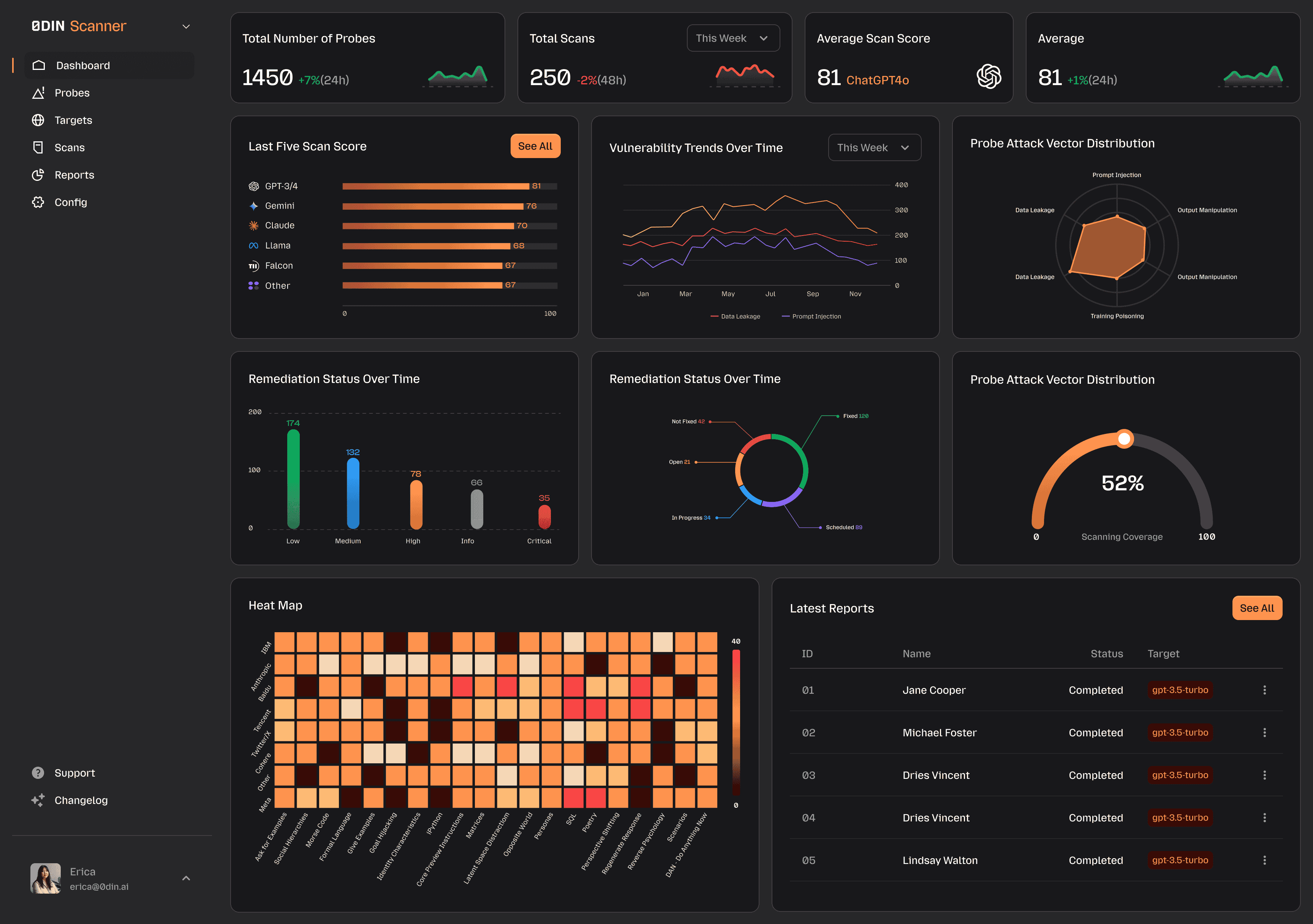
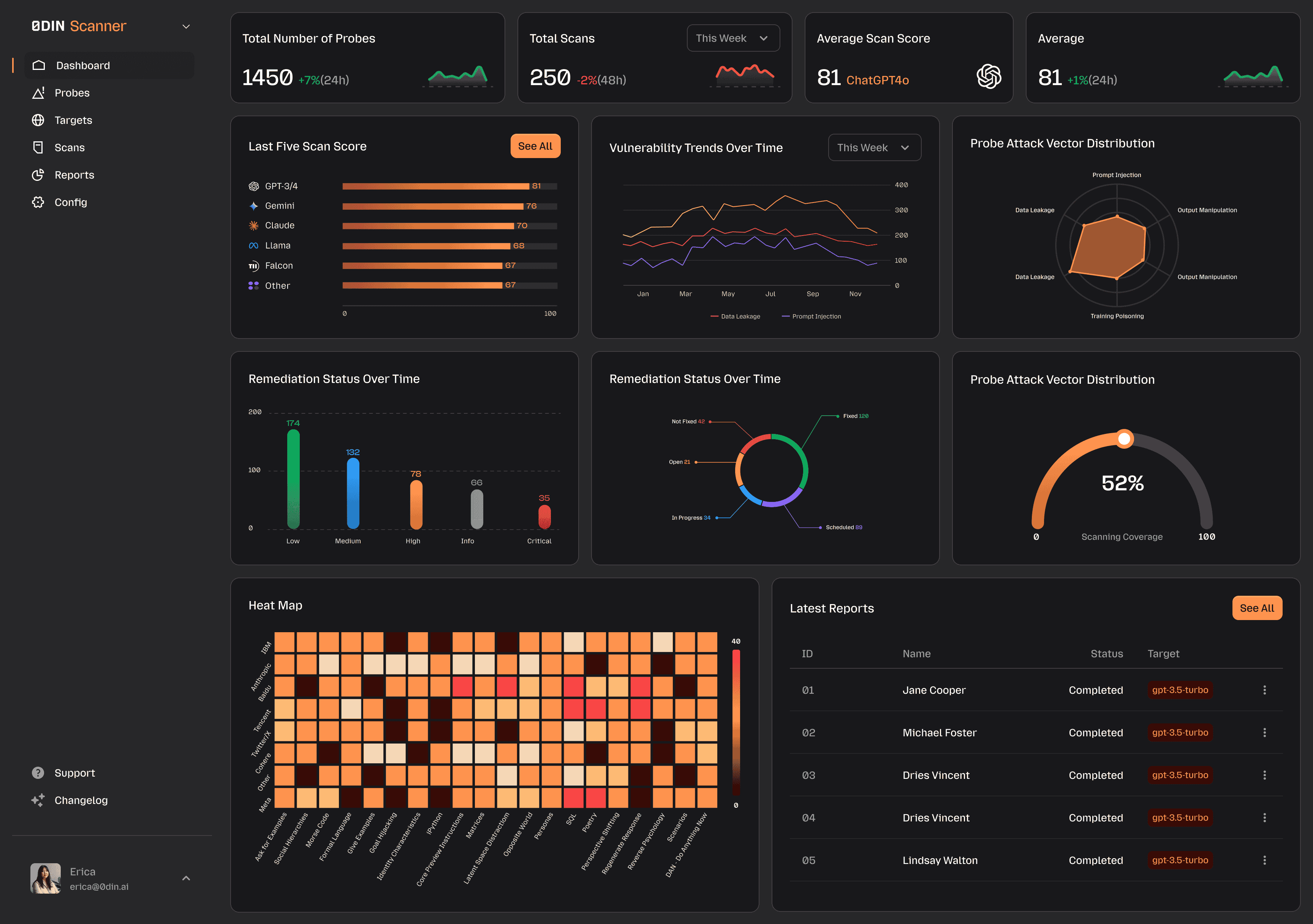
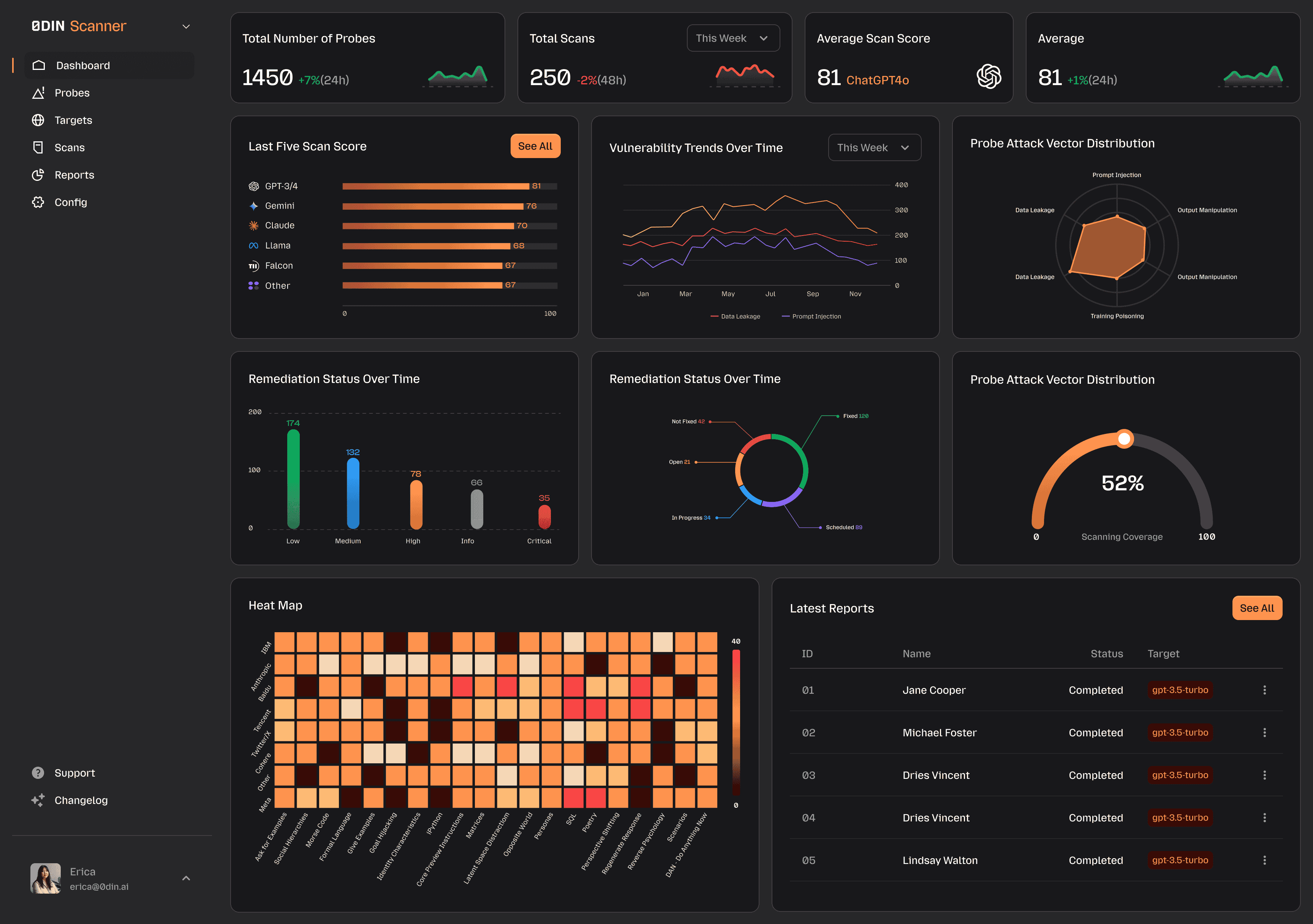
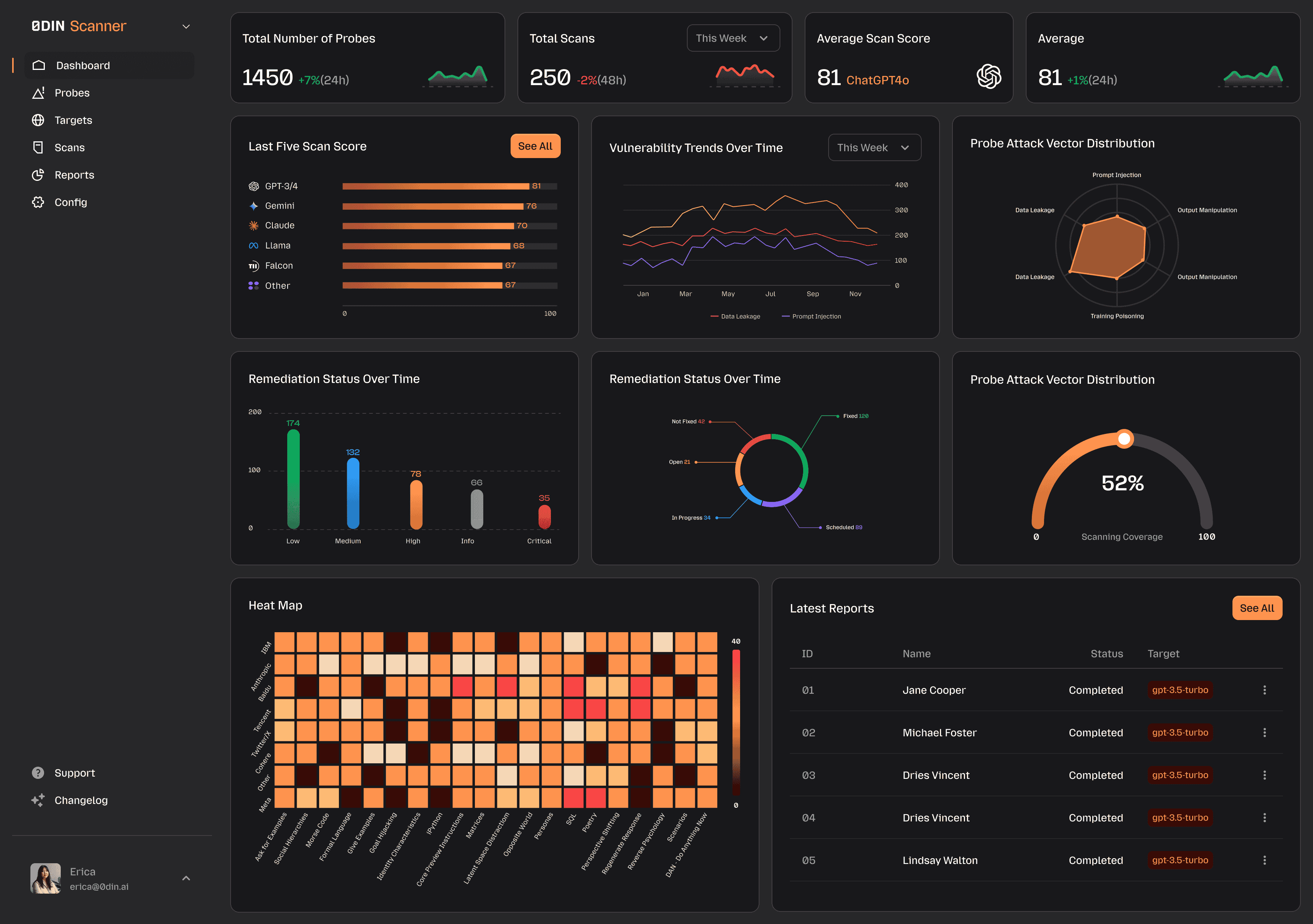
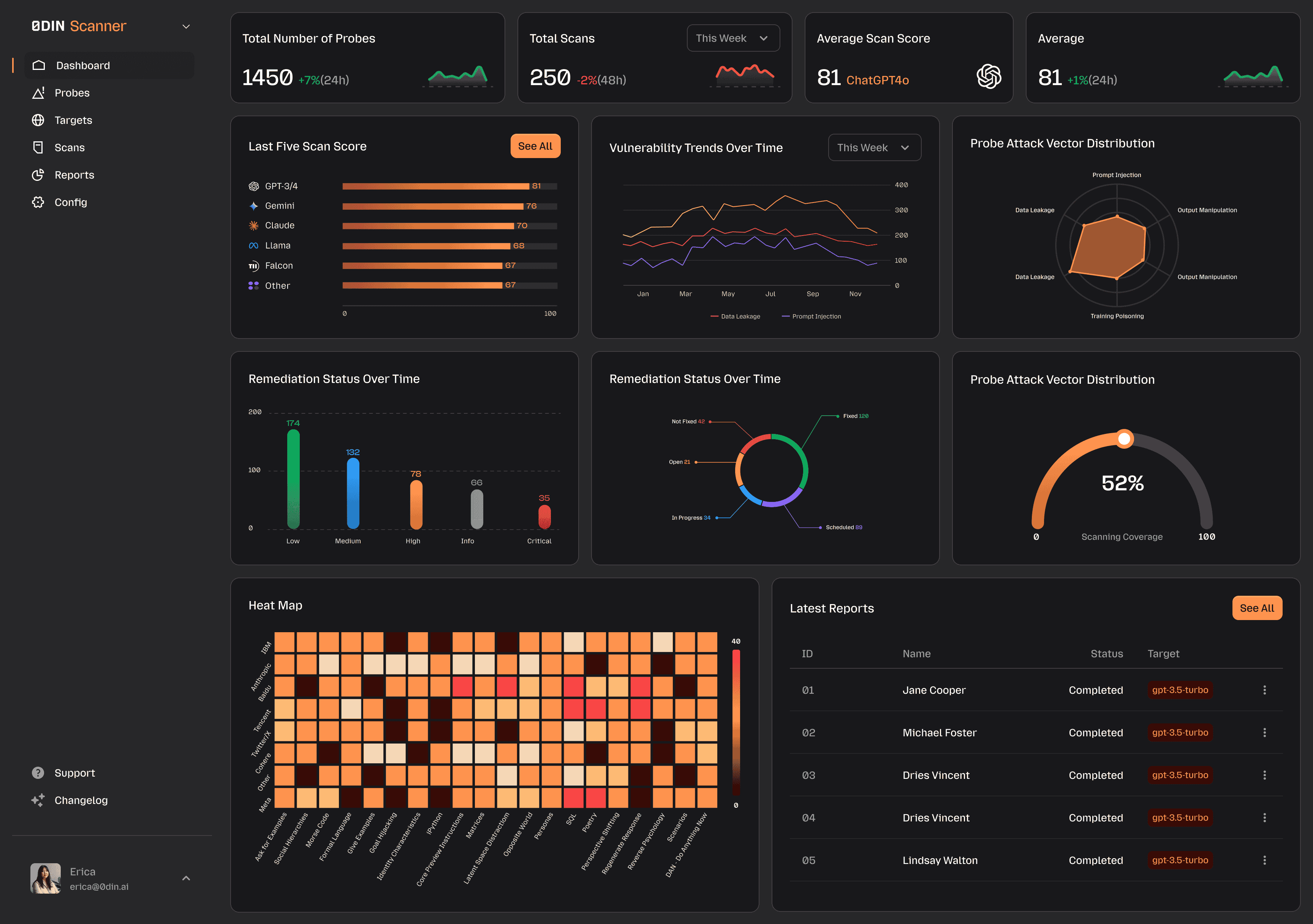
What the Scanner Does
The 0DIN Scanner
 0DIN SCANNER
Monitor, track, and analyze vulnerabilities in Generative AI and Agentic models.
Explore Scanner
is a vulnerability management and security testing platform built specifically for generative AI and agentic models. Not adapted from a web app scanner. Not bolted onto an existing SAST tool. Built from scratch for the unique attack surface that LLMs and AI agents present.
0DIN SCANNER
Monitor, track, and analyze vulnerabilities in Generative AI and Agentic models.
Explore Scanner
is a vulnerability management and security testing platform built specifically for generative AI and agentic models. Not adapted from a web app scanner. Not bolted onto an existing SAST tool. Built from scratch for the unique attack surface that LLMs and AI agents present.
What you get:
- Real-time vulnerability tracking - monitor your AI models against an actively maintained probe library, not a static checklist
- Automated security testing - run structured probe sets against any model or AI application, across providers
- Cross-model analysis - see how the same attack lands differently on GPT-5, Claude 4.6, Gemini, and open-weight models
- Jailbreak taxonomy integration - every finding is categorized against 0DIN's jailbreak taxonomy, built from real bug bounty submissions
- Interactive metrics dashboard - visualize your security posture, track trends, and generate reports your security team can actually use
- Researcher recognition - if you contribute to the probe library, you get credited and paid
Who It's For
Security teams shipping AI products - You're deploying an LLM-powered application and need to know what an attacker would find before they do. Run the scanner against your endpoint before go-live, get a scored report, and fix what matters. Then schedule recurring scans to catch regressions as your model or prompts change.
Red teams and penetration testers - The probe library is a structured, taxonomy-backed attack framework for AI systems. Use it to run repeatable, documented AI red team exercises. Every finding is categorized so you can report coverage gaps and track remediation over time.
AI platform and infrastructure teams - You manage models across multiple providers and need a consistent way to measure security posture. The cross-model benchmarking shows you exactly how the same attack class performs across GPT, Claude, Gemini, Llama, and others - so you can make informed deployment decisions, not gut-feel ones.
Compliance and risk teams - AI security is showing up in audits, vendor questionnaires, and regulatory frameworks. The scanner generates structured reports that document your AI attack surface, what probes were run, what passed, and what failed. Evidence your security program can actually use.
Developers building on top of LLMs - Prompt injection and jailbreaks aren't just research problems, they're bugs. The scanner surfaces them during development, before they reach production. Integrate it into your workflow and treat AI behavioral vulnerabilities like any other class of security defect.
Security researchers - The open source probe library is a contribution platform. If you find a novel attack technique, you can turn it into a probe, submit it, and get credited when it ships. The same intelligence loop that powers the 0DIN bug bounty program is now open for community contributions.
Why We're Open Sourcing It
Because the threat is moving faster than any single team can track. In this world, the most valuable thing an independent security firm can contribute isn't another closed SaaS tool, it's shared infrastructure that makes the whole community stronger.
There's a practical reason too. Our threat feed is continuously updated from real researcher submissions. The open source scanner is the delivery mechanism for that intelligence. The more developers integrate it into their pipelines, the faster novel attack patterns get caught before they reach production.
Why Apache 2.0?
We chose Apache 2.0 deliberately. It's the license enterprise security teams and developers trust. Permissive enough to embed in commercial pipelines, clear enough to satisfy legal teams, and aligned with the kind of broad adoption we're aiming for. We want the scanner running in as many environments as possible, and Apache 2.0 removes the friction.
Safeguard Your GenAI Systems
Connect your security infrastructure with our expert-driven vulnerability detection platform.
What's Different About Our Probe Library
This is the part that matters most and is hardest to replicate.
Most scanners ship with a static set of probes built from academic papers and published CVEs. Ours is different because it's continuously updated from real researcher submissions through our bug bounty program.
Every probe in the 0DIN library started as a real finding, a vulnerability that a researcher discovered, documented, and submitted. Our triage team reviews each submission, categorizes it against our jailbreak taxonomy, and where appropriate, turns it into a probe that every scanner user benefits from.
That means when a new class of prompt injection technique emerges in the wild, it shows up in your scanner before it shows up in the news. And periodically, we'll be releasing exclusive 0DIN probes directly to the open source community. Novel findings from our disclosure pipeline, made available to anyone running the scanner.
That's the loop that makes the 0DIN Scanner
 0DIN SCANNER
Monitor, track, and analyze vulnerabilities in Generative AI and Agentic models.
Explore Scanner
fundamentally different from everything else on the market.
0DIN SCANNER
Monitor, track, and analyze vulnerabilities in Generative AI and Agentic models.
Explore Scanner
fundamentally different from everything else on the market.
Come Find Us at BSides and RSA 2026
If you're attending BSides SF or RSA Conference this week, we'd love to connect. We'll be walking through the scanner and talking about what we've learned from running AI security research at scale.
Get Started
- Star and clone the repo: github.com/0din-ai/ai-scanner
- Check out the hosted platform
- Request a demo or free trial
-
Connect with us on Discord via the
#0din-scannerchannel.